Exchange Online Access
The app must be granted permissions to send emails through your Exchange Online mailboxes. For that, a Global administrator needs to grant the app the permission to send via users' mailboxes. The permissions is granted through a special button on:
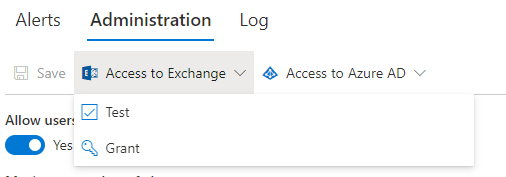
- Alerts -> Administration tab.
- Global Settings -> Alerts
The grant is identical, it doesn't matter where it is granted from.
If the permission is not granted, alerts will not be sent.
Application vs Delegated Permissions
The app can access your Exchange Online with an access token. It can retrieve this token via either one of the following permission grants:
- Application permissions- granted once per tenant by a Global Administrator and provides the application independent access to send emails as any user in the tenant. Not additional grants are needed and the grant does not expire unless manually revoked by a Global Administrator.
- Delegated permissions - granted once per each mailbox. The application is only able to send emails via mailboxes where the permission consent was given.
Your information security team should make a decision which approach works best for your organization. By default, the Application permissions approach is in effect. You can change to delegated approach under Alerts -> Administration.
Note: when switching from Application to Delegated approach, the access token will be retrieved in 2 steps:
- Delegated token is attempted to be retrieved.
- If the token is empty (permission not granted), application token will then be retrieved if possible.
This is done to prevent downtime while all the individual mailbox permissions are granted. Once you are confident all the necessary permissions are in place, you can go ahead and revoke the application permissions. You will do it directly under Enterprise apps in your Entra ID configuration. Make sure to delete the correct enteprise app, as both have the same name. Make sure the Applicaiton (Client) ID of the app to be deleted is 473b3114-9255-4053-862e-23071f19a4b7 (5dea69de-e26a-490a-8395-40e35c3cc20e for GCC High customers).
Application Permissions
The permissions grant page is opened in a pop-up window, please make sure it's allowed to open by your pop-up blocker.
Delegated Permissions
- When using Authorized senders, each authorized sender should be granted beforehand consent (in most cases by an administrator or the mailbox owner). See next section for more information regarding Authorized senders.
- When using user's own email address, the grant is verified and potentially requested when saving each alert. Grant is only given once per tenant. Subsequent alert creation will only verify the existence of the grant. It will not request a new one if it is already valid.
Note: your tenant configuration might block user consent for sending email permission. If so, users won't be able to consent directly, but will be asked to request a permission from an administrator.
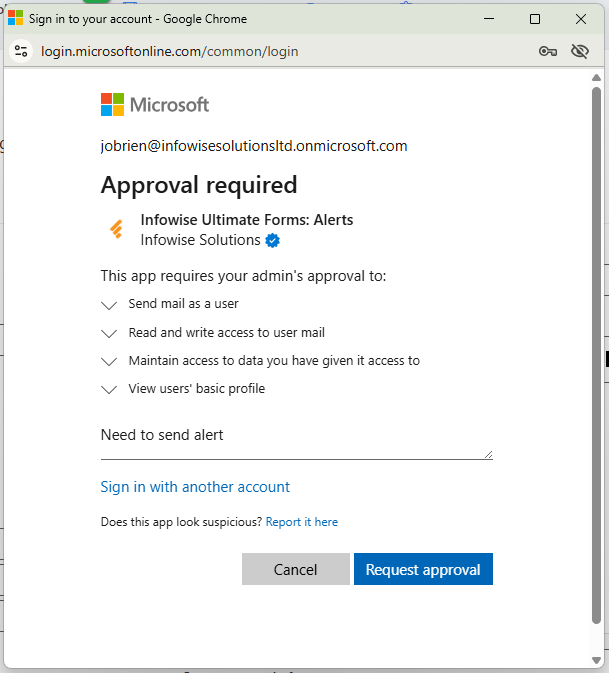
Your security team needs to decide if to allow direct user consent for Mail.Send and Mail.ReadWrite or request approvals each time. You can learn more about user consent in this Microsoft article.
Specifying sender mailbox
By default, alerts can only be sent from the mailbox of the alert creator. If you would like to send from a different account, you would need to configure a list of Authorized senders at a site collection (Alerts -> Administration) or tenant level (Global Settings). Tenant-level settings can also override and block site collection level settings.
To specify Authorized senders at a site collection level:
- Open the main page for alert management as a site collection administrator and a Global Administrator of the tenant.
- Switch to Administration tab
- Check "Allow changes to sender".
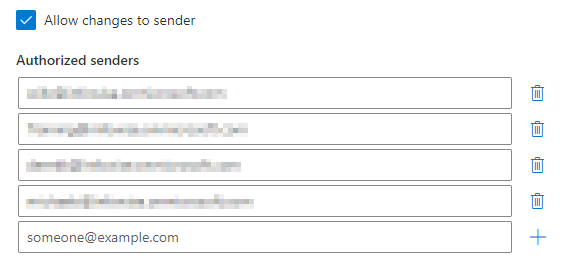
- Specify authorized senders. Each one has to be an existing mailbox in your Exchange Online. Note: distribution list emails are not supported.
- Site collection administrators can, if allowed by the tenant administrator, now enter any valid mailbox email and regular users can only pick from authorized senders specified at site collection or tenant level.
Tenant-level settings are similar, except for being accessed from Global Settings -> Alerts.
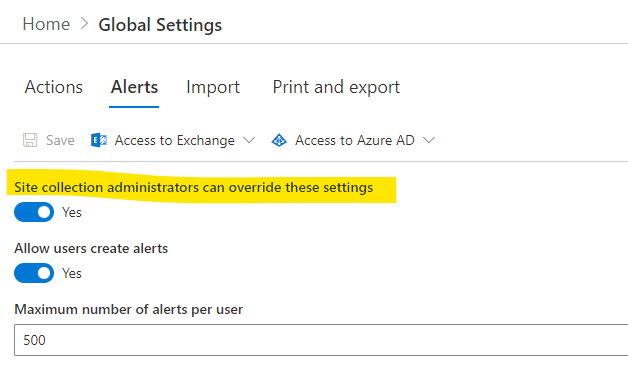
Site collection settings override tenant (Global) settings, unless tenant setttings disallow that.
Security Trimming
By default, the app will ensure that every recipient who is a tenant user has at least Read access to the item. If such access cannot be determined, the recipient is removed. Note that by default we cannot check membership of Azure Entra ID groups. To enable that, a global administrator must grant the app the right to query group membership in Entra ID. The permission is granted via a special button under Alerts -> Administration or Global Settings.
You can also disable security trimming at site collection or tenant level.